Cyber attacks enlist innocent PC owners
Hijacked machines used to jam Web sites
Investigators are piecing together details about one of the most aggressive computer attacks in recent memory – a powerful “denial-of-service” assault that overwhelmed computers at U.S. and South Korean government agencies, companies and institutions, in some cases for days.
Here are some questions and answers about the attack.
Q. What is a “denial-of-service” attack?
A. If you and all your friends called the same restaurant over and over and ordered things you didn’t really want, you’d jam the phone lines and overwhelm the kitchen to the point that it couldn’t take any more new orders. That’s what happens to Web sites when criminals hit them with denial-of-service attacks. They’re knocked offline by too many junk requests from computers controlled by the attackers.
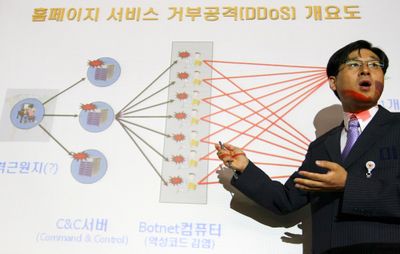
The bad guys’ main weapons in such an attack are “botnets,” or networks of “zombie” personal computers they’ve infected with a virus.
The virus lets the criminals remotely control innocent people’s machines, which are programmed to contact certain Web sites over and over until that overwhelms the servers that host the sites.
The servers become too busy to respond to anything, and the Web site slows or stops working altogether.
Q. How often do these attacks happen?
A. People try denial-of-service attacks all the time – many government and private sites report being hit every day. Often the assaults are unsuccessful, because Web sites have ways of identifying and intercepting malicious traffic.
Denial-of-service attacks are noisy by design and intend to make a statement. They’re not subtle attempts to infiltrate a Web site’s defenses, which can be much more insidious because that gives hackers access to whatever confidential information is stored there.
Often the attacks take a site out for a few hours, before Web site administrators can respond. But the most recent attack was widespread and went on for a while, beginning over the July Fourth weekend and running into this week.
Q. Some organizations appear to have fended off these recent attacks, while other Web sites went down. How can this be?
A. The sites that went down probably were less prepared, because they are less accustomed to being hit or aren’t sensitive enough to warrant extra precautions.
Popular Web sites, like e-commerce and banking sites, have a lot of experience dealing with denial-of-service attacks, and they have sophisticated software designed to identify malicious traffic.
Q. Is there usually evidence of who the culprits were?
A. It’s usually easier to stop a denial-of-service attack than it is to figure out who’s behind it.
Simply identifying where the malicious traffic is coming from won’t get investigators very far, because the infected PCs that get roped into a botnet are owned by innocent people who don’t know their computers are being used for nefarious purposes.
Q. If these attacks make use of compromised computers corralled into a “botnet,” should I be worried about whether my PC is one of them? What could I do to prevent that or fix it?
A. If your computer is being used in a denial-of-service attack, you’re likely to see a significant slowdown, because your processing power is being siphoned for the assault.
But there aren’t always obvious signs that your computer has been infected.
So the best thing is to focus on prevention, namely by having up-to-date antivirus software.
In particular, make sure your antivirus software gets updated over the next few days.
If you’re concerned your machine might be infected, it’s wise to run an antivirus scan. Many antivirus companies offer a free scan from their Web sites.